Understanding the Aftermath: What Happens to Your Data When It’s Stolen?

Introduction Our digital era has brought forth both incredible conveniences and potent threats, one of the most severe being data breaches. In a recent multinational police operation, an ID marketplace notorious for selling stolen credentials was shut down. The operation, aptly named “Operation Cookie Monster,” resulted in 120 arrests, including ten Australians. The scope of […]
Understanding Dark Web Scanning: An Essential Cybersecurity Tool

The dark web carries serious threats to businesses. One such threat is the exposure of sensitive data. Dark web scanning is a cybersecurity measure that detects and mitigates this risk. Defining the Dark Web The dark web is an internet sector not indexed by standard search engines. Accessing it requires specific software like Tor. Despite […]
Mitigating Your Biggest Risk: Why Human Error Shouldn’t Define Your Cyber security
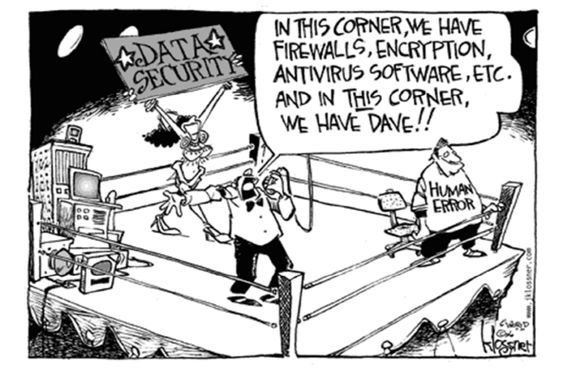
Human error poses significant risks to cyber security in today’s digital world. Unintentional actions or mistakes by employees can lead to data breaches, phishing attacks, and other security incidents. To address this challenge, organisations must prioritise user training and awareness sessions. In this article, we delve into the importance of mitigating human error in cyber […]
The Power of End User Training and Awareness Sessions

Employees are the first line of defense against cyber threats. End user training and awareness sessions play a vital role in equipping employees with the knowledge and skills needed to protect sensitive data and mitigate risks. In this blog post, we explore the importance of these sessions and how they empower employees to become proactive […]
Empowering Board Resilience: Unleashing the Power of Board Cyber Event Simulations

Board members hold a critical role in navigating the ever-changing landscape of cyber threats. To fortify their resilience, board cyber event simulations have emerged as a transformative tool. In this blog post, we explore the invaluable role of these simulations in preparing boards to tackle cyber threats head-on and empower them with the confidence to […]
Safeguarding Confidentiality and Trust: The Importance of Data Privacy and Protection

Data privacy and protection are paramount in today’s digital landscape, where organizations handle vast amounts of sensitive information. Protecting customer data, intellectual property, and other confidential information is crucial for maintaining trust and compliance with privacy regulations. In this article, we explore the significance of data privacy and protection and how it safeguards confidentiality and […]
